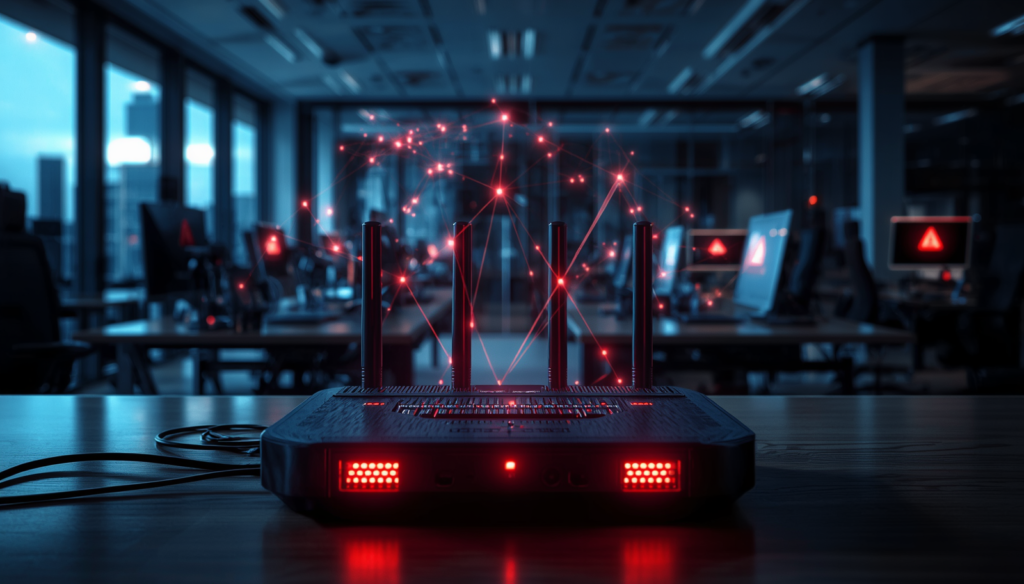
Russia’s Router Hack Is a Business Warning: Why Outdated Network Hardware Can Put Your Company at Risk
Most businesses think cyberattacks begin with a phishing email, a malicious download, or ransomware spreading through employee devices.
But the latest Russia-linked router hacking campaign shows a different and more uncomfortable reality: sometimes attackers do not need malware at all. Sometimes all they need is outdated hardware, poor patching habits, and a network device nobody has thought about in years.
According to the story, hackers linked to Russia’s military intelligence used known flaws in older routers to steal Microsoft Office authentication tokens from users across thousands of networks. Instead of installing malicious software, they changed DNS settings on vulnerable routers and intercepted authentication traffic after users had already logged in successfully.
That makes this more than just another cybersecurity incident.
It is a business lesson.
Because what this story really reveals is how easily neglected infrastructure can undermine expensive software, modern security tools, and even multi-factor authentication.
What happened
Microsoft and security researchers said the campaign involved a Russia-backed threat actor known as Forest Blizzard, also referred to as APT28 or Fancy Bear. At the peak of its activity in December 2025, the operation reportedly affected more than 18,000 routers, many of them older, unsupported, or badly outdated devices, especially models sold into the small office and home office market.
The attackers reportedly focused on older Mikrotik and TP-Link routers and used known vulnerabilities to modify DNS settings. Once those settings were changed, users on those networks could be redirected in ways that allowed attackers to intercept OAuth authentication tokens tied to Microsoft services such as Outlook on the web.
That is what makes this attack especially dangerous.
The attackers did not need to phish every employee individually. They did not need to drop malware onto every device. They simply compromised the network layer and let normal user behavior do the rest.
Why this matters for business
This story matters because it highlights a blind spot many organizations still have, they invest heavily in cloud tools and endpoint security, but ignore the aging network hardware connecting employees to those systems.
A business may feel secure because it uses Microsoft 365, requires multi-factor authentication, and has antivirus protection in place. But if traffic is being manipulated before it reaches those systems, that entire security posture becomes weaker.
The real lesson is simple: your business is only as secure as the least-maintained device on your network.
The business risks this story exposes.
- Old hardware can quietly break modern security
Many organizations still treat routers as basic utility devices. As long as the internet works, nobody pays much attention to them.
That mindset is dangerous.
This incident shows that outdated routers can become entry points into business systems, even when the company is using modern cloud software and identity tools.
A neglected router in a branch office, satellite location, or executive’s home office can create a serious exposure point for the entire business.
- Remote and hybrid work expanded the attack surface
One of the most important takeaways from this case is how much business risk now sits outside the traditional office.
The story notes that many of the targeted routers were in the small office and home office category. That means remote workers, small teams, contractors, and satellite operations may be relying on consumer-grade equipment that is outdated, unsupported, or poorly configured.
For businesses, that changes the equation.
Home office infrastructure is no longer just a personal setup. In many cases, it is part of the company’s security perimeter.
- “No malware” does not mean “no compromise”
This attack is a reminder that businesses cannot rely only on traditional malware detection to feel safe.
In this case, the attackers reportedly did not need to install malware on the routers. They changed DNS settings and intercepted authentication tokens instead.
That means businesses focused only on endpoint alerts may completely miss this type of intrusion.
If your security strategy is built mostly around catching malicious files, suspicious downloads, or ransomware behavior, you may still be exposed to network-level attacks that look far quieter but are just as damaging.
- MFA is essential, but it is not the finish line
Many companies assume multi-factor authentication solves most account security problems.
It helps a great deal, but this case shows why it is not enough by itself.
Because the attackers intercepted authentication tokens after the user had already logged in and completed MFA, they could potentially access those accounts without needing to steal passwords or one-time codes directly.
For business leaders, the takeaway is clear: identity security cannot stop at login. Companies need stronger session controls, conditional access, token revocation processes, and ongoing monitoring for suspicious behavior after authentication.
- End-of-life infrastructure is now a leadership issue
Older routers often stay in service for one simple reason: they still seem to work.
But “working” and “secure” are not the same thing.
Unsupported devices, delayed firmware updates, and weak lifecycle management are no longer minor IT housekeeping problems. They are operational risks that can affect email, communications, account access, data protection, and business continuity.
That makes hardware replacement and patch discipline business decisions, not just technical ones.
What smart businesses should do now
This story should push companies to take a much broader view of cybersecurity.
Here are the most important actions businesses should consider:
Audit all routers and edge devices.
Create a full inventory of routers, firewalls, and network appliances across offices, branch locations, and remote work environments.
Replace unsupported hardware.
Any router that is end-of-life or no longer receiving security updates should be removed from active use.
Review DNS and admin settings.
Check for unauthorized DNS changes, weak administrator passwords, exposed management access, and unusual configuration activity.
Standardize remote-work network security.
For employees handling sensitive information, especially finance, legal, HR, and executive teams, set minimum standards for home office networking equipment and security.
Strengthen identity security beyond MFA.
Use conditional access policies, device trust controls, session monitoring, token revocation capabilities, and anomaly detection to reduce post-login risk.
Update incident response plans.
Make sure your cyber response playbooks account for attacks that do not involve malware and may originate from compromised infrastructure instead of compromised endpoints.
What this means for business leaders
The biggest message here is not just that Russian-linked hackers compromised routers.
It is that attackers are still finding success through the boring, overlooked parts of business infrastructure.
Companies often spend the most attention on visible technology: cloud apps, AI tools, productivity software, dashboards, and software subscriptions. But attackers are often looking lower in the stack, at the forgotten hardware underneath everything else.
That is where weak operational discipline becomes a business vulnerability.
If you are a business owner, executive, operations leader, or IT decision-maker, this story is a reminder to ask harder questions:
Do we know every router currently in use across the business?
Are any of those devices outdated or unsupported?
How much of our remote workforce is using consumer-grade hardware?
Could we detect a compromise that does not involve malware?
Are we protecting user sessions after login, not just passwords before login?
Those questions matter because the next major breach may not begin with a sophisticated phishing campaign.
It may begin with a router nobody remembered to replace.
Final thoughts
This incident is not just a cybersecurity headline. It is a business warning.
The companies that stay resilient in the years ahead will not just be the ones with the newest software. They will be the ones that manage the full security picture, from cloud applications all the way down to the physical devices connecting employees to those systems.
In today’s environment, outdated infrastructure is not just an IT oversight.
It is a business risk hiding in plain sight.